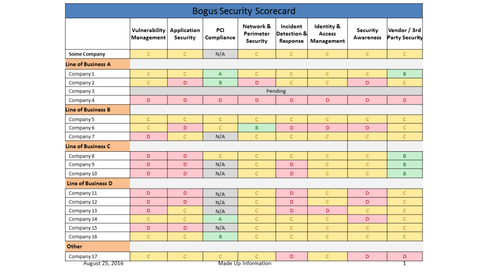
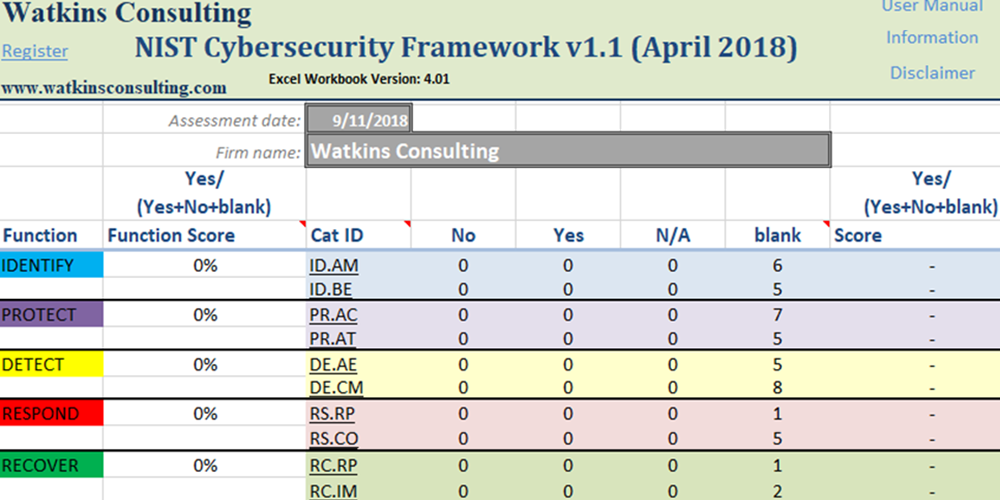
Cyber Security Scorecard Template

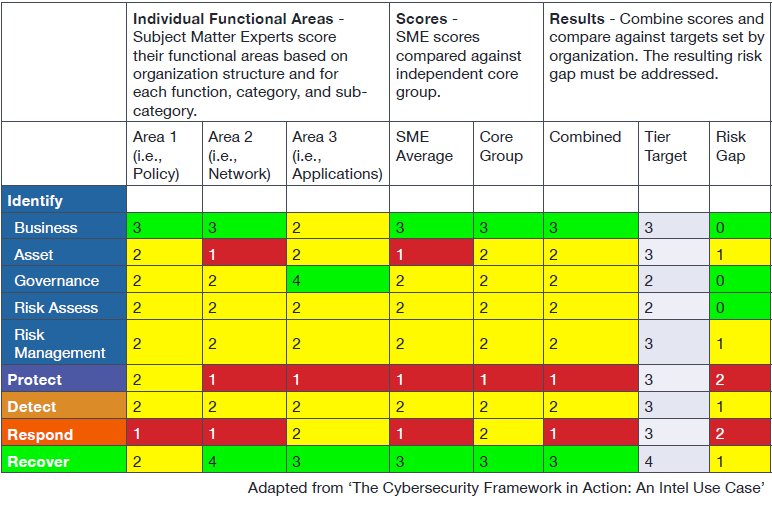
The public power cybersecurity scorecard is an online self assessment tool for public power utilities to assess cyber risk plan improvements prioritize investments and benchmark their security posture.
Cyber security scorecard template. Total isat and pii per usda from departments scorecard 833 826 826 826 820 820 819 819 813 027 027 024 fy17 specialized role based training complete total 13 124 19 19 19 19 19 19 na na na na. The spreadsheet alone is not sufficient for you to choose suitable information security metrics nor to develop a workable security measurement system. The forrester new wave. Instant securityscorecard offers you a free high level overview of your organizations cybersecurity across 10 key risk factors including network security application security patching cadence and moreview sample report.
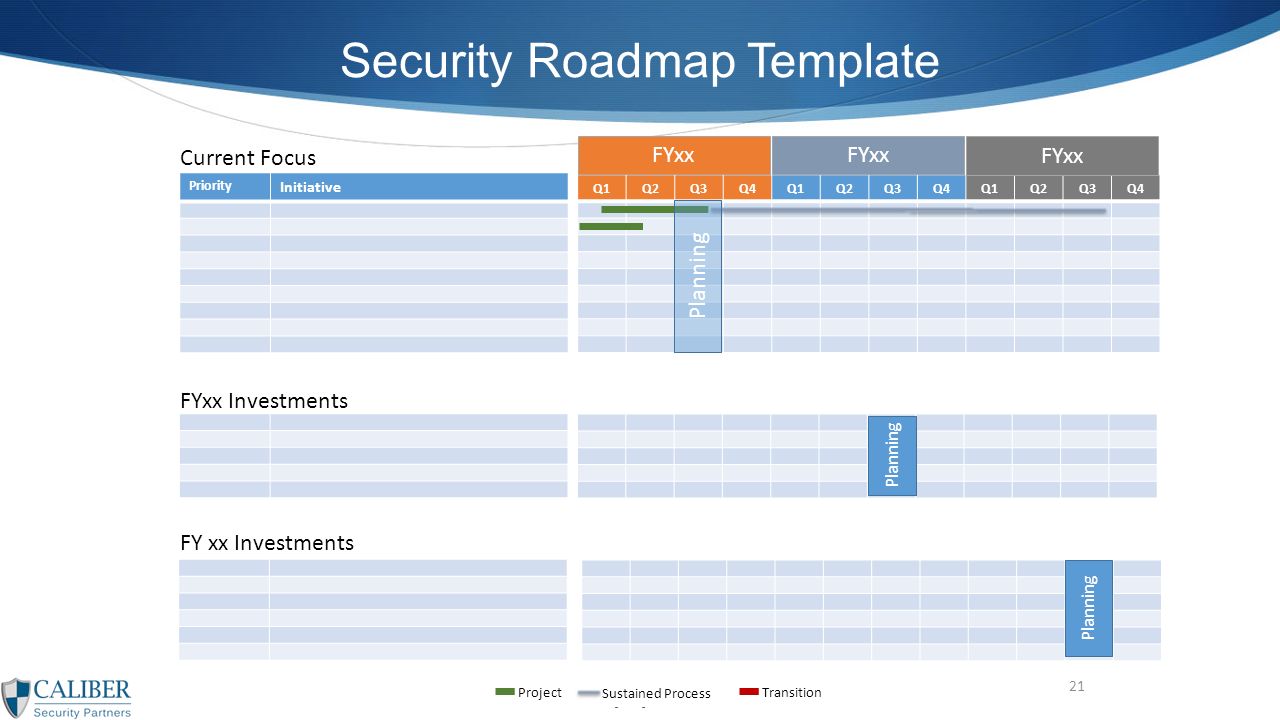
Download this new forrester analyst report to gain bleeding edge insight into what security risk ratings can do for your organization today and why securityscorecards offering leads the pack. The security scorecard will then become a valuable tool for routine and sustainable executive communication. Impairment of the reliability of it restriction of its availability and the breach of. Why would a cfo or cio want to see a scorecard.
1 cyber security is the endeavor to prevent damage by disruption outage or misuse of it and if damage does occur the repair of this damage. The book describes a rational process to score rank and shortlist candidate information security metrics and goes on to cover the complexities of designing using and maintaining a metrics system. The damage may consist of. The addition of new out files into data repository in sharepoint intranet will trigger an event that will invoke extract transform load etl packages in sql server.
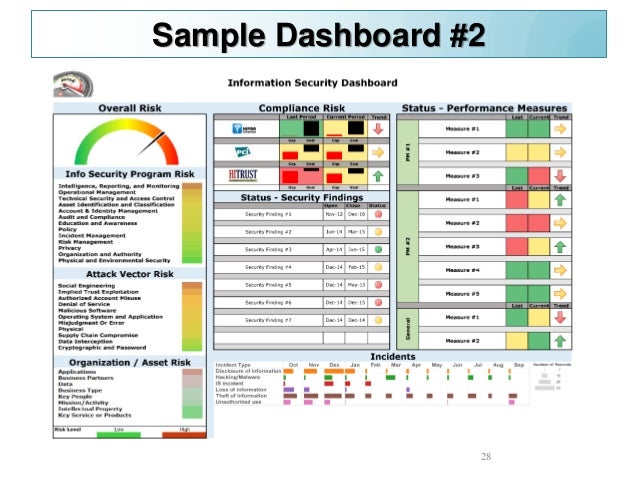
What is the ci cybersecurity dashboard. Source the source data of the dashboard will originate from the output of several cyber monitoring tools. The software automatically generates a recommended action plan when any issues are discovered and clearly shows your historical data. Securityscorecards security ratings allow you and your organizations business stakeholders to enables users to continuously monitor the most important cybersecurity kpis for your company and your third parties.
Discover how hackers partners and customers see your organization from the outside instantly.