Ssh Certificate Management

In ssh key management is primarily around login access and certificate management is around access to applications websites and other resources scaff said.
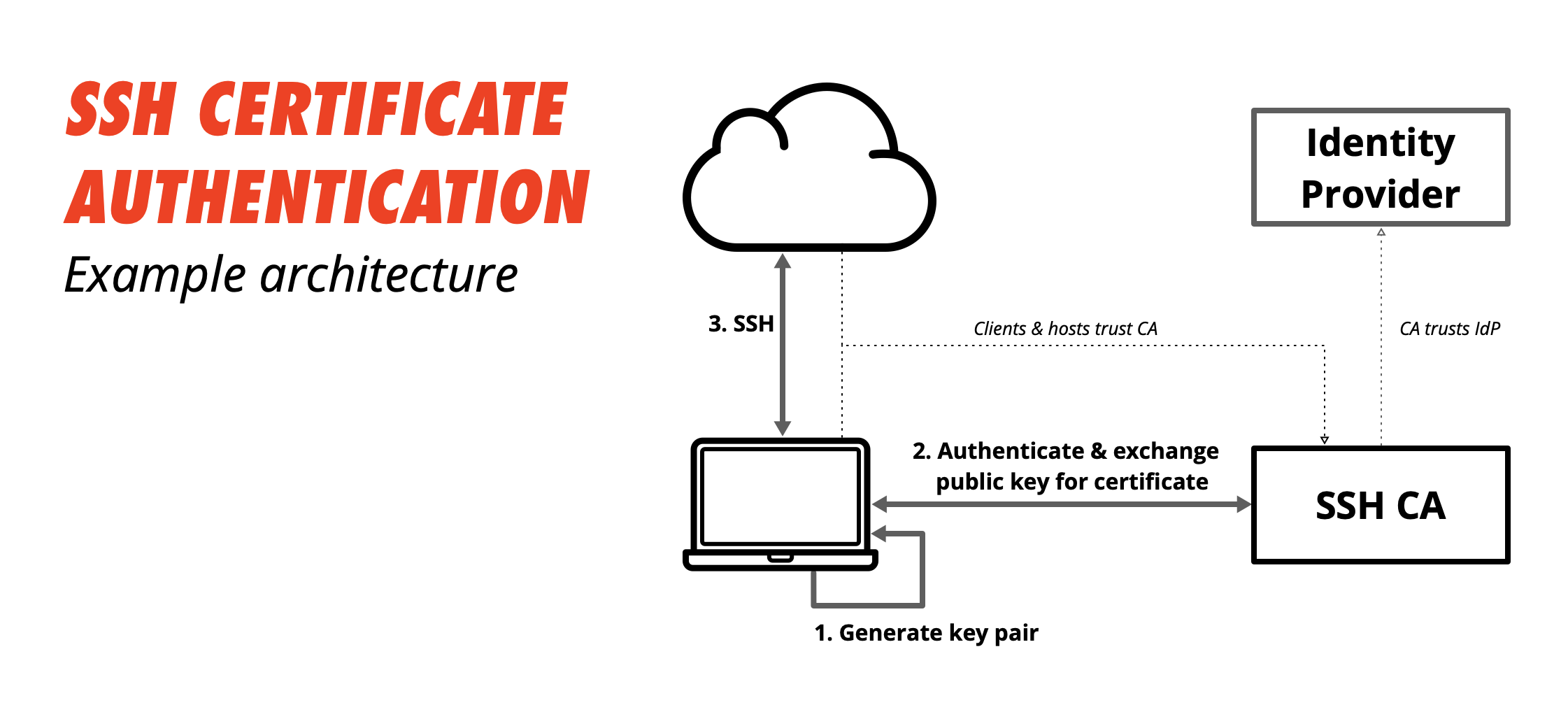
Ssh certificate management. An ssh certificate is simply a public key signed by a well known trusted entity called a certificate authority ca. Certificate management we design best of breed commercial solutions for secure access that help our customers win in the global data economy. I was thinking about making a root ca and signing certs and then configuring vms to allow anyone presenting a cert signed by the ca. Ssh secure shell is used in every data center and in every major enterprise.
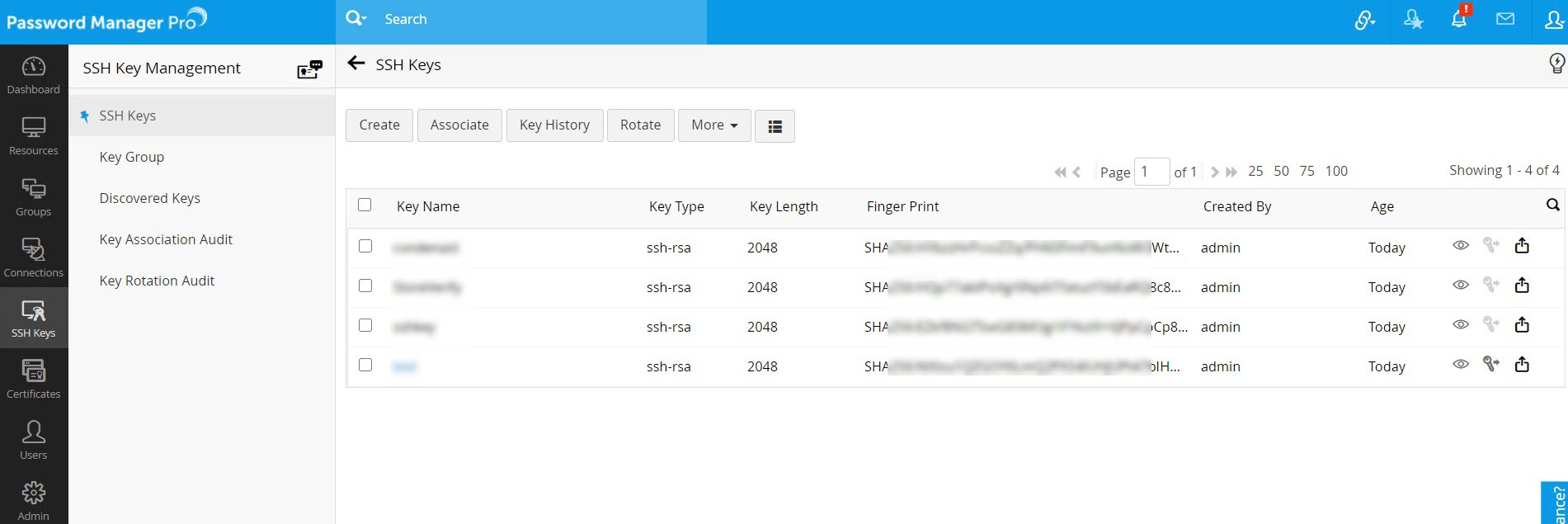
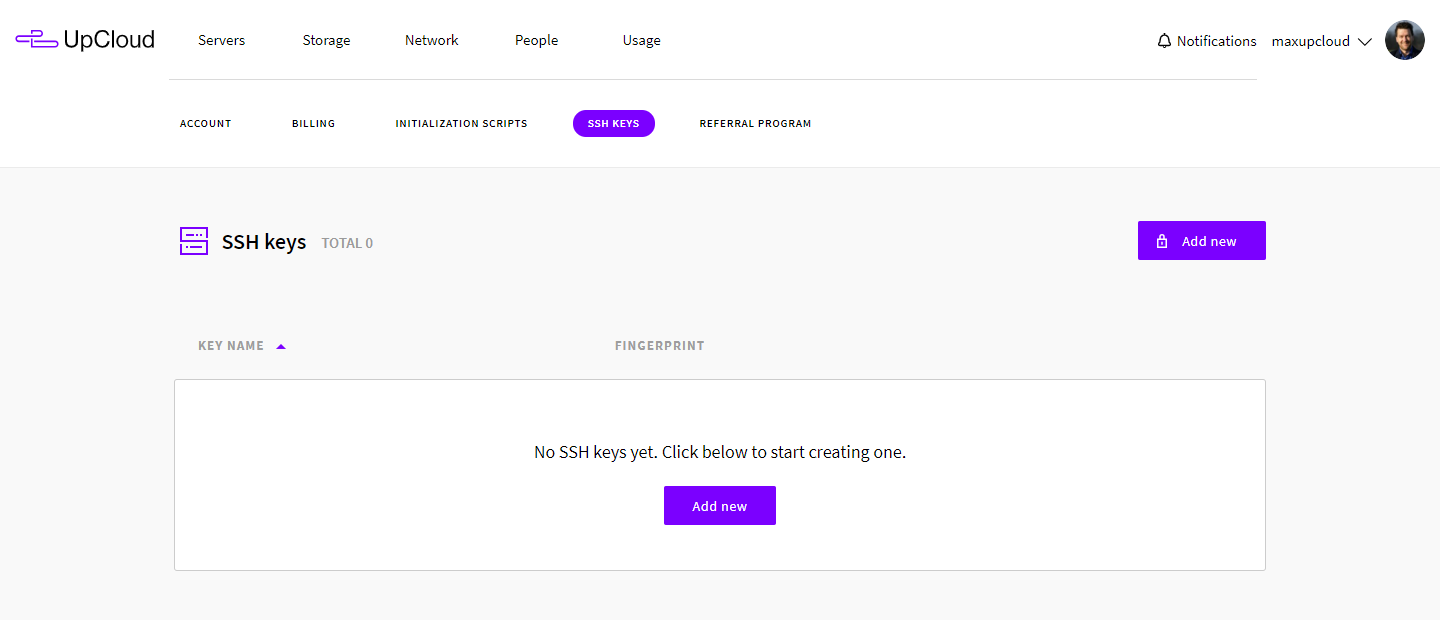
You need visibility into how ssh keys are used so that you can detect these threats and defend against them. Sshcom is one of the most trusted brands in cyber. The ssh protocol is the global gold standard for remote system administration and secure file transfer. How do you guys manage your certificates across vms.
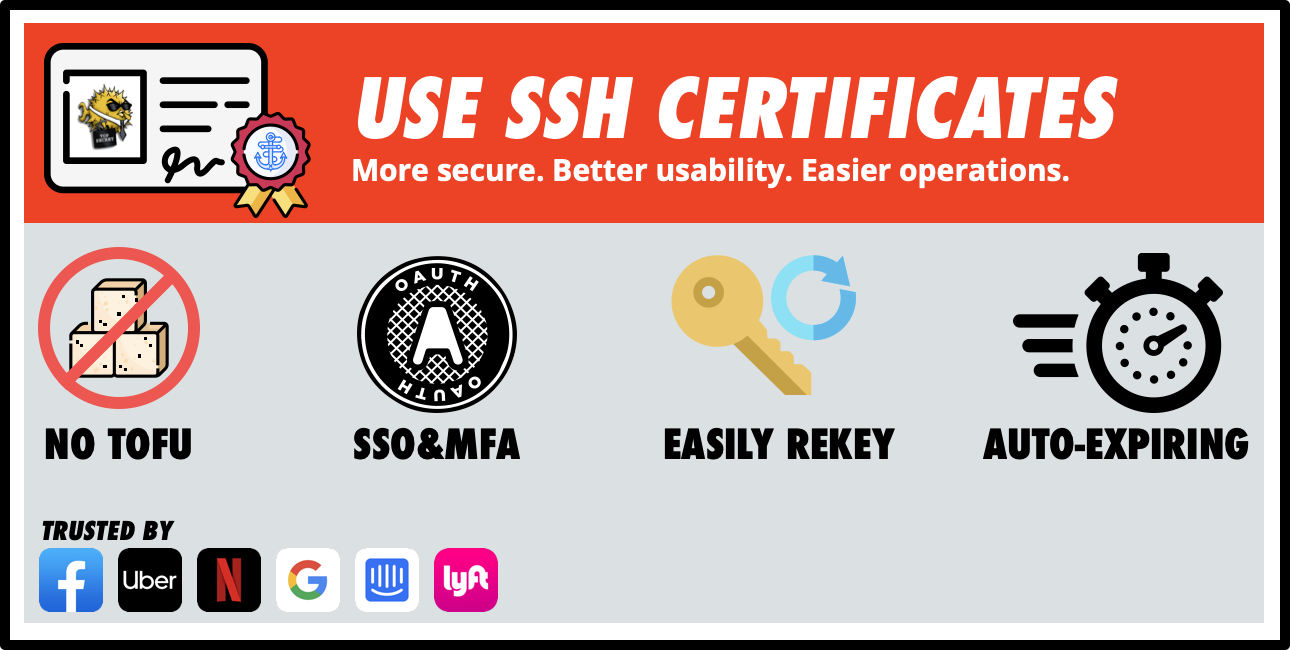
One of the features behind the immense popularity of the protocol is the strong authentication using ssh keys. The format of the certificate is described in usrsharedocopenssh version protocolcertkeys. Simplify compliance requirements for keys and certificates. Venafi helps you successfully meet compliance requirements for protecting keys and certificates.
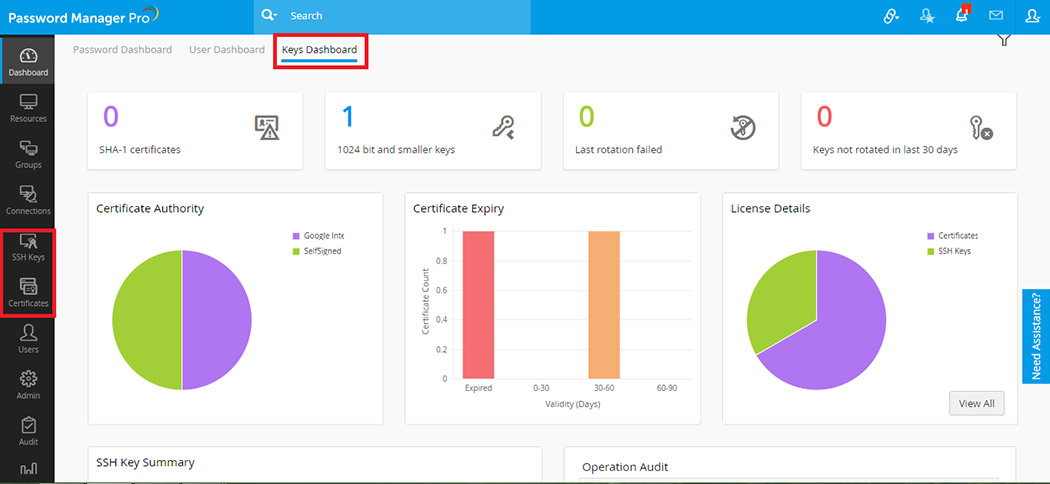
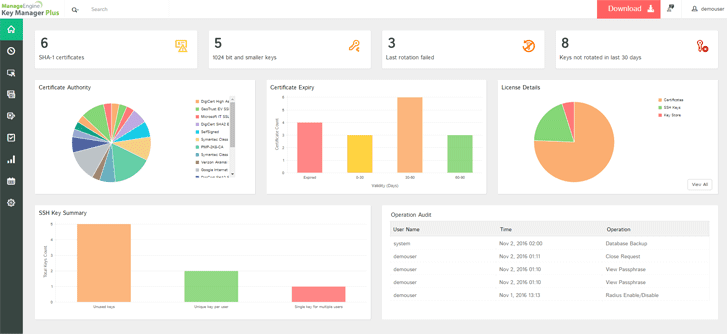
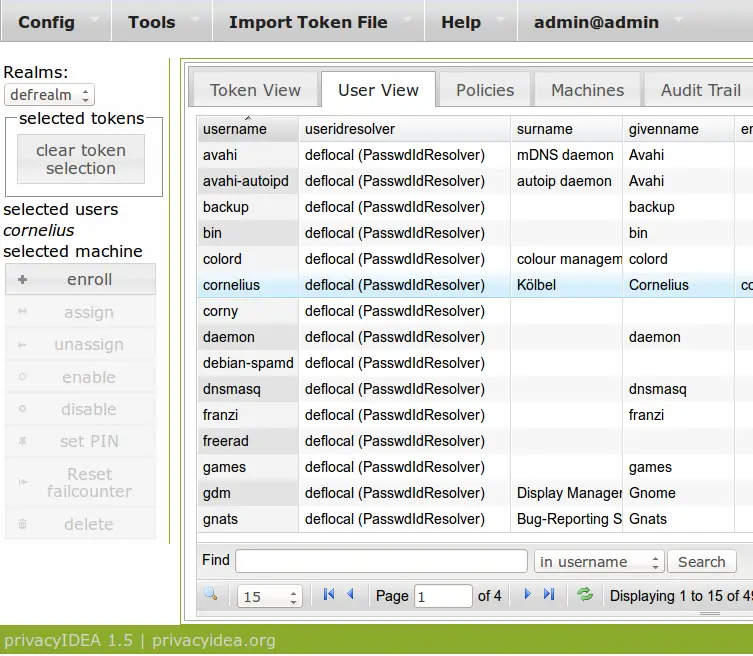
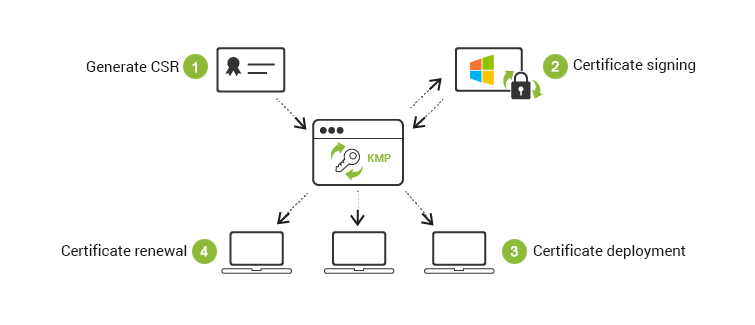
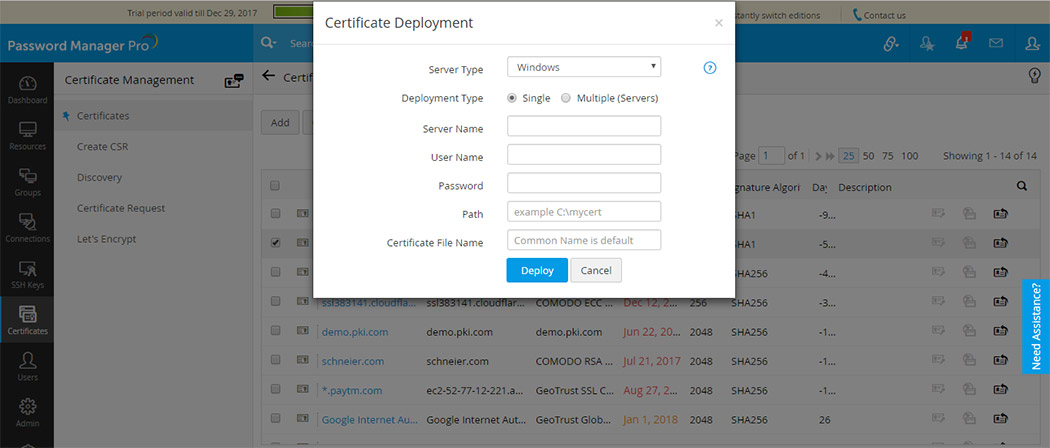
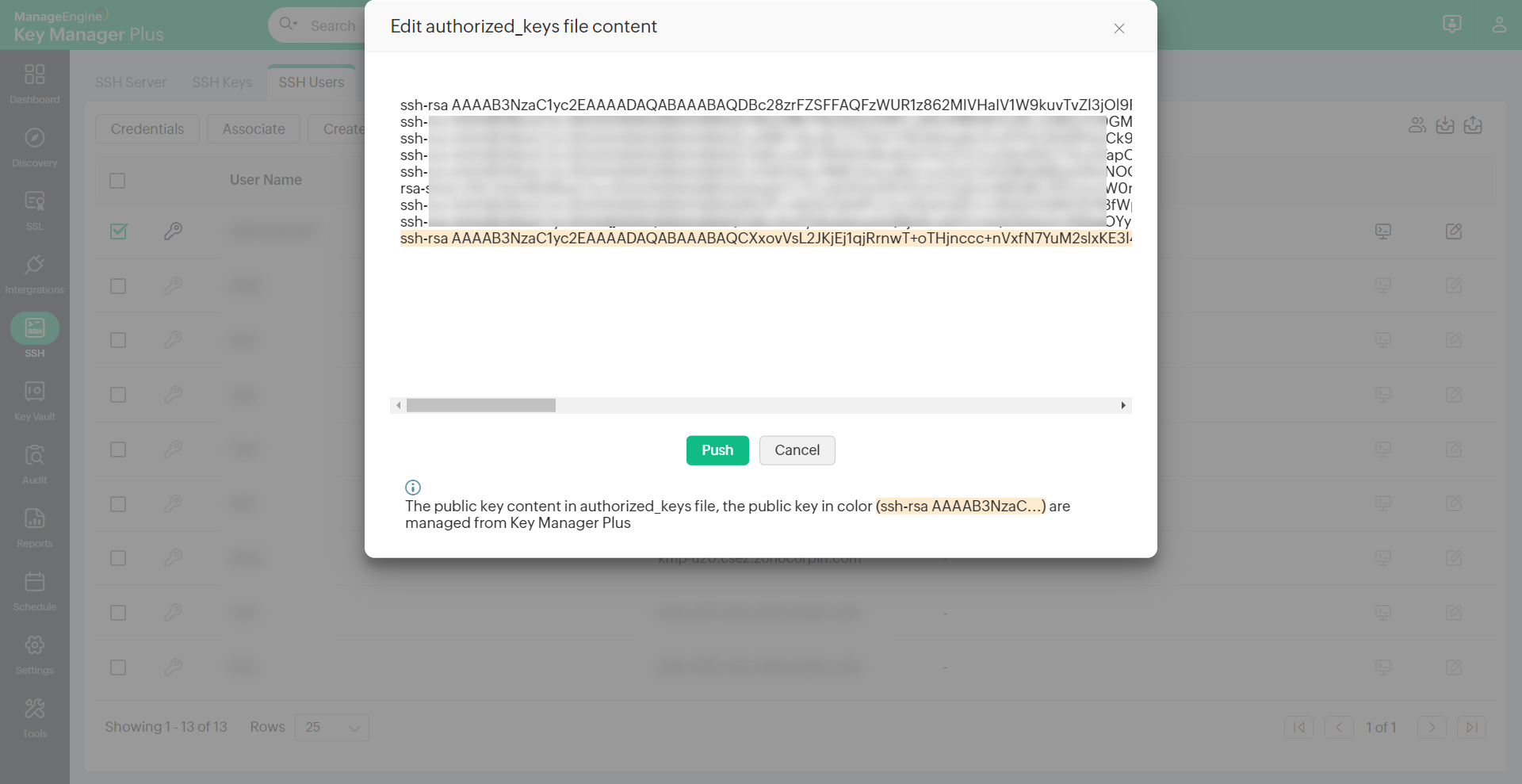
The process of managing and securely administering cryptographic keys in a crypto ecosystem is commonly referred to as ssh key management. Web based ssh key and ssl certificate management solution for enterprises manageengine key manager plus is a web based key management solution that helps you consolidate control manage monitor and audit the entire life cycle of ssh secure shell keys and ssl secure sockets layer certificates. This means that copying keys around is no longer necessary. Our certificate management workload dropped almost immediately by about.
Companies require ssh key management to oversee the creation generation storage exchange protection replacement and crypto shredding of ssh keys to maintain crypto ecosystem security. Openssh certificates contain a public key identity information and validity constraints. Certificate management we design best of breed commercial solutions for secure access that help our customers win in the global data economy. They are signed with a standard ssh public key using the ssh keygen utility.
Users and servers simply must agree on which ca to trust. Is this bad practice.